IBM is doing its best to keep its Domino HTTP Server updated to accommodate all of the security patches and enhancements that are more readily available in competing web servers such as Apache and NGinx. One of these security enhancements is adding Security Headers or HTTP Response Headers to Domino’s HTTP server.
The main headers needed currently are:
Strict-Transport-Security
Referrer-Policy
X-Frame-Options
X-Content-Type-Options
X-XSS-Protection
Content-Security-Policy
Starting with Domino 9.0.1 Feature Pack 6 (or FP6) you can now add the majority of the above headers directly to Domino using both Notes.ini settings and an Internet Site Document. The IBM stated limitation is that a maximum of 4 Headers can be accommodated by Domino since you can add only one header using the Notes.ini and 3 to the Internet Site document. However, we’ve found that the limit is actually 5 since the “Strict Transport Security” header can be added as a separate Notes.ini setting.
For the Internet Site document you’ll have to pick and choose which headers you want to add since you do have that 3 header limit. Based on our testing and experience, we’ve found that the one header that causes the most problems to your site after applying it is the “Content Security Policy”. For sites with complex applications running X-Pages and other scripting technologies, this latter header can cause certain functions to break, so we decided to leave that one out of the 5 that we added. Your experience may be different and you may decide that you want that one added instead of another header.
You can add the following entries to the Notes.ini to support Strict-Transport-Security and X-Frame-Options (after saving your Notes.ini you will need to restart your Domino server for these to take effect):
HTTPDisableServerHeader=1
HTTP_HSTS_MAX_AGE=17280000
HTTP_HSTS_INCLUDE_SUBDOMAINS=1
HTTPAdditionalRespHeader=X-Frame-Options: SAMEORIGIN
To add the following 3 headers you can do so using the Internet Site Document and creating an Website HTTP Response Header Rule:
Referrer-Policy
X-Content-Type-Options
X-XSS-Protection
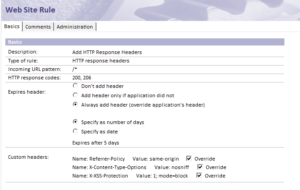
If you don’t already use an Internet Site document created for your web server then you will need to create one and change the settings on the server document in the Basics tab to point to the newly created Internet Site document (instructions on how to create an Internet Site document are beyond the scope of this post). If you’ve created a new Internet Site document or already have an existing one then the next step is to create an HTTP Response Header Rule (HTTP responses headers is a “type of rule” for a Web Site Rule document) which is under that same document. When creating an HTTP Response Header Rule you set the following values:
Description: Whatever description you want here
Type of Rule: HTTP response headers
Incoming URL Pattern: /*
HTTP response codes: 200, 206
Expires header:
Always add header (override applcation’s header)
Specify as number of days (selected)
Custom Headers (see table below and attached image):
[su_table]
| Name | Value | Override |
| Referrer-Policy | same-origin | Checked |
| X-Content-Type-Options | nosniff | Checked |
| X-XSS-Protection | 1; mode=block | Checked |
Once you have filled in the Web Site Rule correctly, save and close it.
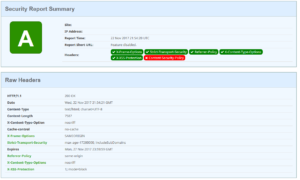
 After it is saved you can restart the Domino HTTP task to activate the new rules (you don’t need to restart the whole Domino server). Once the HTTP task is restarted you can go to the following website to scan and check the status of your domain and all 5 headers except Content-Security-Policy should now be recognized and you should have an “A” rating assigned (please see attached image for similar results):
After it is saved you can restart the Domino HTTP task to activate the new rules (you don’t need to restart the whole Domino server). Once the HTTP task is restarted you can go to the following website to scan and check the status of your domain and all 5 headers except Content-Security-Policy should now be recognized and you should have an “A” rating assigned (please see attached image for similar results):
https://securityheaders.io
Here are all five of the settings and their corresponding values:
Strict-Transport-Security: max-age=31536000; includeSubDomains
Referrer-Policy: same-origin
X-Frame-Options: SAMEORIGIN
X-Content-Type-Options:nosniff
X-XSS-Protection: 1; mode=block
Another way to add security headers is to add a reverse proxy in front of your Domino server. The reverse proxy can reside on the same server as the Domino server or separately in the DMZ to provide additional security. Setting up a reverse proxy to add the http response readers is for a future topic.

 888-614-2197
888-614-2197 sales@caicorp.com
sales@caicorp.com
Leave a Reply